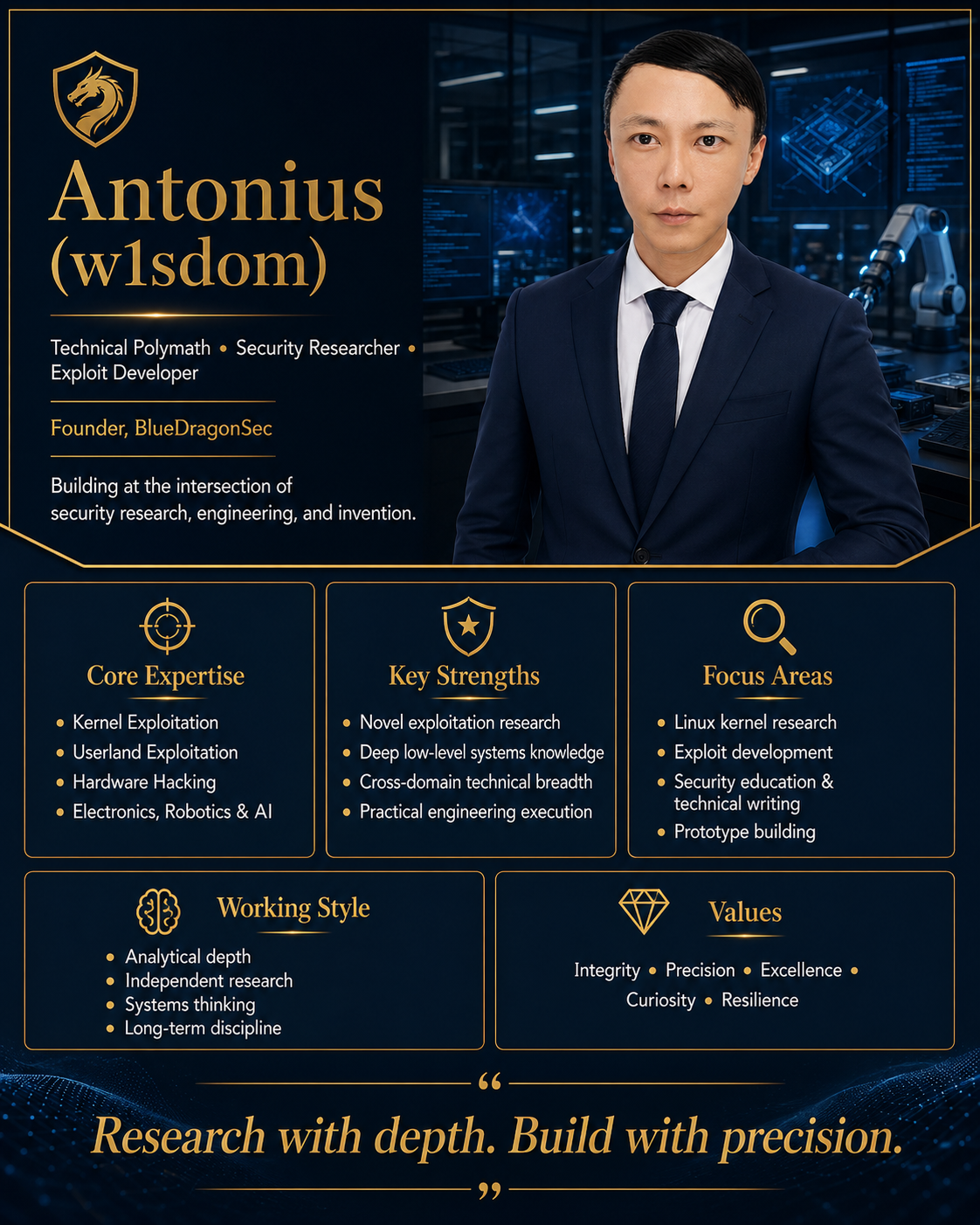
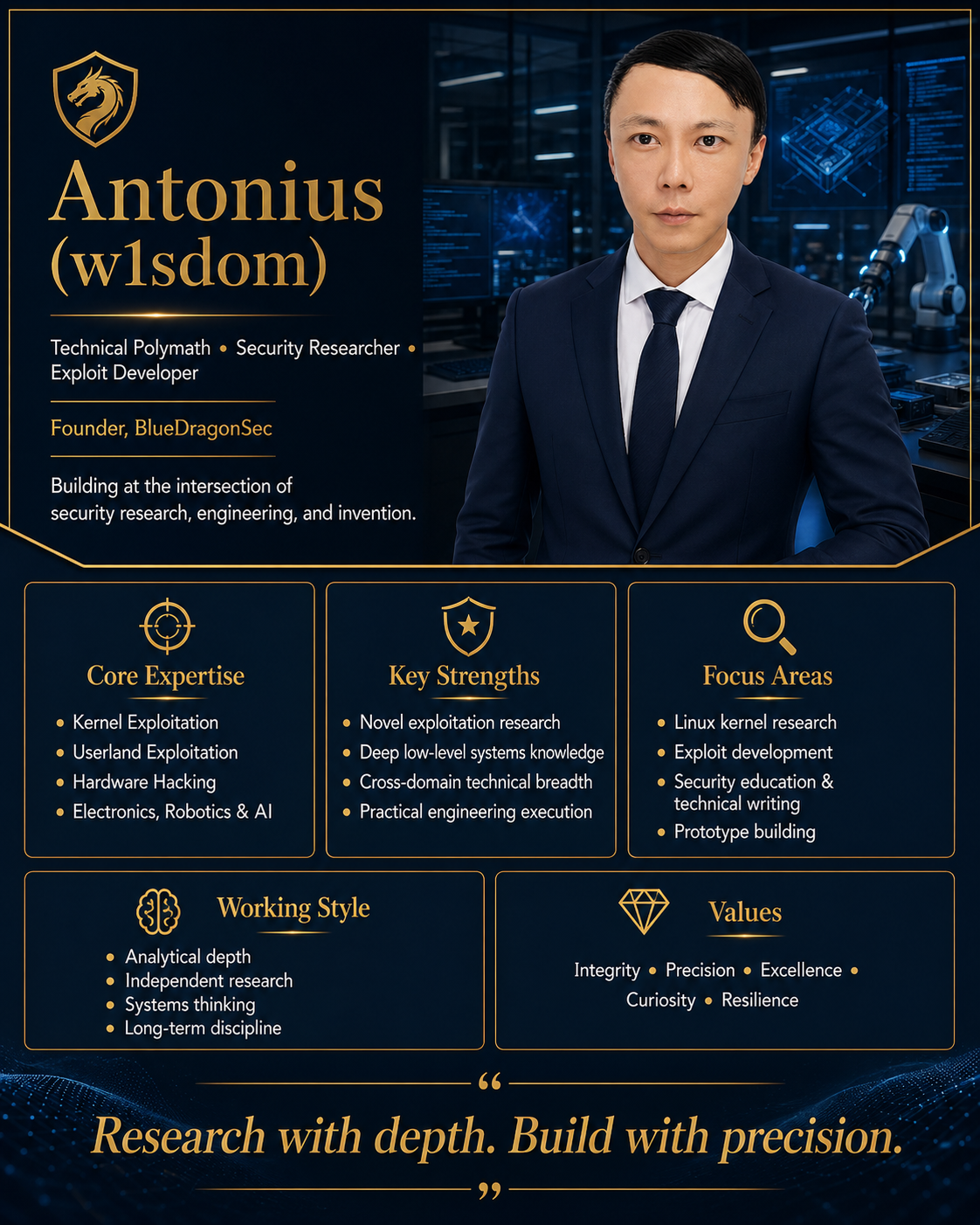
Who is Antonius (w1sdom)?
This is the personal web of Antonius Wisdom, a security researcher based in Indonesia. I do low level vulnerability research & hardware hacking.
Hobbies
Low Level · Hardware Hacking · w1sdom
A former 1990s assembly virus writer. As a polymath security researcher, I combine multidisciplinary expertise in low-level vulnerability research and hardware hacking, supported by a solid foundation in mechatronics, mathematics, and deep learning to provide a rare skillset.
This is the personal web of Antonius Wisdom, a security researcher based in Indonesia. I do low level vulnerability research & hardware hacking.
Hobbies